Security policy
1 INTRODUCTION
1.1 JUSTIFICATION OF THE INFORMATION SECURITY POLICY
WOCU MONITORING, S.L. relies on ICT (Information and Communication Technology) systems to achieve its objectives. These systems must be managed diligently, taking appropriate measures to protect them against accidental or deliberate damage that may affect the availability, integrity, or confidentiality of the information processed or the services provided.
The objective of information security is to guarantee the quality of information and the continuous provision of services by acting preventively, monitoring daily activity, and reacting swiftly to incidents.
ICT systems must be protected against rapidly evolving threats with the potential to impact the confidentiality, integrity, availability, intended use, and value of information and services. To defend against these threats, a strategy is required that adapts to changing environmental conditions to ensure the continuous provision of services. For this reason, the National Security Framework (Royal Decree 311/2022 of January 8, hereinafter ENS), in its Article 11, establishes that “All senior bodies of Public Administrations must formally possess their security policy, which shall be approved by the head of the corresponding senior body.”
This implies that the different areas of the organization must apply the minimum security measures required by the National Security Framework, as well as continuously monitor service delivery levels, follow and analyze reported vulnerabilities, and prepare an effective response to incidents to guarantee the continuity of the services provided.
All areas must ensure that ICT security is an integral part of every stage of the system’s life cycle, from its conception to its retirement from service, including development or procurement decisions and operational activities. Security requirements and funding needs must be identified and included in planning, requests for proposals, and tender specifications for ICT projects. Departments must be prepared to prevent, detect, react to, and recover from incidents, in accordance with Article 7 of the ENS.
1.3 OBJECTIVES AND SCOPE OF THE SERVICES PROVIDED
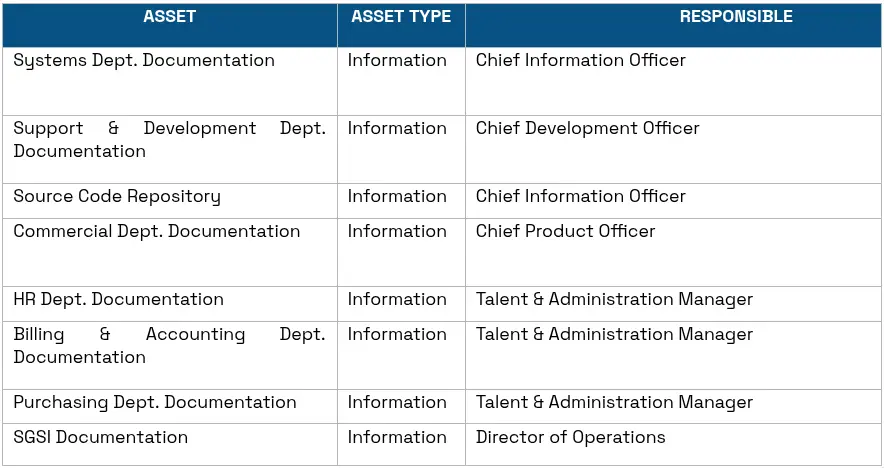
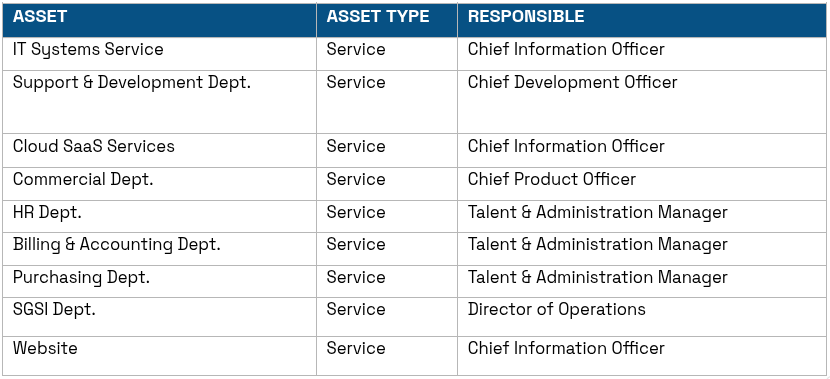
This Security Policy applies to the various services provided in its daily activity, specifically:
- Design
- Development
- Support and maintenance
The specific scope of the ENS (National Security Framework) is as follows: Information system applied to:
“Design, development, and support and maintenance of digital infrastructure monitoring solutions in large facilities”
It assumes its commitment to information security, committing to its proper management in order to offer all its stakeholders the highest guarantees, with the following objectives:
- Guarantee the quality of information and the continuous provision of services, acting preventively, monitoring daily activity, and reacting swiftly to incidents.
- Ensure the rapid and efficient recovery of services in the face of any physical disaster or contingency that may occur and put the continuity of operations at risk.
- Prevent information security incidents to the extent that it is technically and economically viable, as well as mitigate the information security risks generated by our activities.
- Guarantee the confidentiality, integrity, availability, authenticity, and traceability of information.
- Protect information from potential threats, in a way that ensures the continuity of business lines.
- Minimize potential damages caused.
- Maximize return on investment and business opportunities.
2 REGULATORY FRAMEWORK
As a regulatory basis for the creation of this security guide, the current legislation affecting the development of activities—which explicitly implies the implementation of security measures in information systems—has been analyzed. The legal framework regarding information security is established by the following legislation:
- Royal Decree 311/2022, of May 3, which regulates the National Security Framework (ENS).
- Royal Decree 4/2010, of January 8, which regulates the National Interoperability Framework in the field of E-Government. Its purpose is to create the necessary conditions to guarantee an adequate level of technical, semantic, and organizational interoperability of the systems and applications used by Public Administrations, allowing the exercise of rights and the fulfillment of duties through electronic access to public services, while improving effectiveness and efficiency.
- Regulation (EU) 2016/679 of the European Parliament and of the Council, of April 27, 2016, on the protection of natural persons with regard to the processing of personal data and on the free movement of such data (hereinafter GDPR).
- Organic Law 3/2018, of December 5, on the Protection of Personal Data and guarantee of digital rights.3
3 SECURITY ORGANIZATION
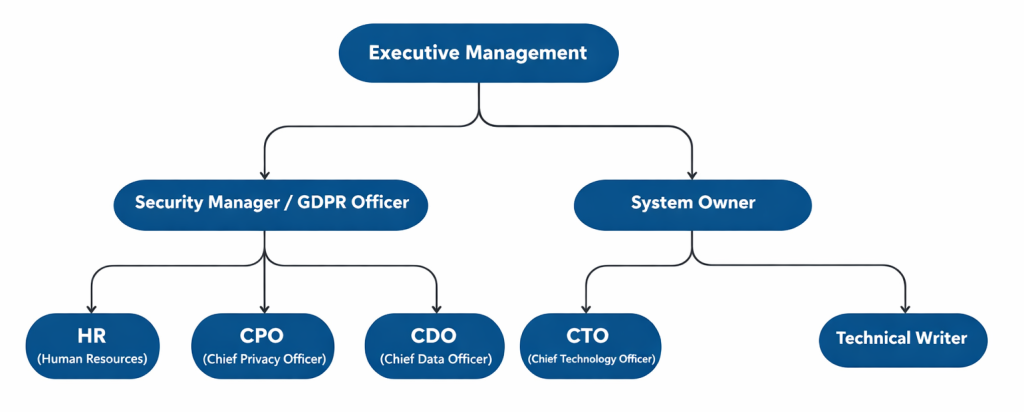
As indicated in Article 12 of the ENS, security must involve all members of the organization. According to Annex II of the ENS, section 3.1, the Security Policy must identify clear roles responsible for ensuring its compliance and must be known by all members of the administrative organization. The following roles are established within the organization in relation to Information Security:
A. Information Owner
The role of the Information Owner has the following functions:
- Adopt necessary technical and organizational measures to guarantee the security of personal data processing and prevent its alteration, loss, or unauthorized processing or access, taking into account the state of technology, the nature of the stored data, and the risks to which they are exposed, whether arising from human action or the physical or natural environment.
- Hold ultimate responsibility for the use made of certain information and, therefore, for its protection.
- The Information Owner is ultimately responsible for any error or negligence leading to a confidentiality or integrity incident.
- Establish information security requirements. Within the framework of the ENS, this equates to the power to determine information security levels.
- Determine the security levels for each dimension within the framework established in Annex I of the National Security Framework (ENS).
- Although the formal approval of the levels corresponds to the Information Owner, they may request a proposal from the Security Officer and should ideally consider the opinion of the System Owner.
B. Service Owner
The heads of the functional units have been designated as Service Owners, and they are responsible for the following functions:
- Regarding the GDPR, by delegation of the Data Controller, the Service Owner is entrusted with the development of tasks related to the management of personal data processing carried out specifically within their area.
- Establish service security requirements. Within the framework of the ENS, this equates to the power to determine information security levels.
- Hold ultimate responsibility for the use made of specific services and, therefore, for their protection.
- The Service Owner is ultimately responsible for any error or negligence leading to a service availability incident.
- Determine the security levels for each dimension of the service within the framework established in Annex I of the National Security Framework (ENS).
- Although the formal approval of the levels corresponds to the Service Owner, they may request a proposal from the Security Officer and should ideally consider the opinion of the System Owner.
- Service delivery must always meet the security requirements of the information it handles, meaning information security requirements can be inherited, while adding requirements for availability, accessibility, interoperability, etc.
C. Information Security Officer
Aquí tienes la traducción al inglés de las funciones del Responsable de Seguridad de la Información:
The main functions entrusted to the Information Security Officer are:
- Coordinate and control the measures defined in the Record of Processing Activities and, in general, ensure compliance with the security measures detailed in the Data Protection Impact Assessment (DPIA).
- Report directly to the Information Security Committee.
- Act as Secretary of the Information Security Committee.
- Convene the Information Security Committee, gathering all relevant information.
- Maintain the security of the information handled and the services provided by the information systems within their scope of responsibility, in accordance with the Organization’s Security Policy.
- Promote training and awareness regarding information security within their scope of responsibility.
- Collect the security requirements from the Information and Service Owners and determine the System category.
- Conduct the Risk Analysis.
- Prepare a Statement of Applicability based on the required security measures according to Annex II of the ENS and the results of the Risk Analysis.
- Provide the Information and Service Owners with information regarding the expected residual risk level after implementing the treatment options selected in the risk analysis and the security measures required by the ENS.
- Coordinate the preparation of the System Security Documentation.
- Participate in the preparation of the Information Security Policy within the framework of the Information Security Committee for approval by Management.
- Participate in the preparation and approval of Information Security regulations within the framework of the Information Security Committee.
- Prepare and approve Information Security Operating Procedures.
- Periodically provide the Security Committee with a summary of security actions, information security incidents, and the status of system security (specifically the level of residual risk to which the system is exposed).
- Prepare Security Improvement Plans alongside the System Owners for approval by the Information Security Committee.
- Prepare Training and Awareness Plans for personnel regarding Information Security, which must be approved by the Information Security Committee.
- Validate the System Continuity Plans prepared by the System Owner, which must be approved by the Information Security Committee and periodically tested by the System Owner.
- Approve the guidelines proposed by System Owners to consider Information Security throughout the entire life cycle of assets and processes: specification, architecture, development, operation, and changes.
- Convene the meetings of the Information Security Committee.
- Prepare the topics to be addressed in Committee meetings, providing timely information for decision-making.
- Draft the minutes of the meetings.
- Be responsible for the direct or delegated execution of the Committee’s decisions.
D. System Owner
The main functions entrusted to the System Owner are:
- Develop, operate, and maintain the Information System throughout its entire life cycle, including its specifications, installation, and verification of its correct operation.
- Define the topology and management system of the Information System, establishing the criteria for use and the services available within it.
- Ensure that specific security measures are properly integrated within the general security framework.
- The System Owner may agree to suspend the handling of certain information or the provision of a certain service if informed of serious security deficiencies that could affect the fulfillment of established requirements. This decision must be agreed upon with the affected Information Owners, the affected Service Owners, and the Security Officer before being executed.
- Apply the security operating procedures developed and approved by the Security Officer.
- Monitor the security status of the Information System and report it periodically—or in the event of relevant security incidents—to the Information Security Officer.
- Develop System Continuity Plans to be validated by the Information Security Officer and coordinated and approved by the Information Security Committee.
- Conduct periodic exercises and tests of the System Continuity Plans to keep them updated and verify their effectiveness.
- Develop guidelines for considering Information Security throughout the entire life cycle of assets and processes (specification, architecture, development, operation, and changes) and provide them to the Information Security Officer for approval.
E. System Security Administrator
The main functions entrusted to the Information System Security Administrator are:
- Implement, manage, and maintain the security measures applicable to the Information System.
- Ensure strict compliance with the established security controls.
- Ensure that traceability, audit trails, and other required security logs are enabled and recording at the desired frequency, in accordance with the Organization’s established security policy.
- Apply Security Operating Procedures and required security mechanisms and services to the Systems, users, and other related internal and external assets and resources.
- Ensure that approved procedures for managing the Information System and the required security mechanisms and services are applied.
- Manage, configure, and update, where applicable, the hardware and software supporting the Information System’s security mechanisms and services.
- Supervise hardware and software installations, modifications, and upgrades to ensure that security is not compromised.
- Approve changes to the current Information System configuration, guaranteeing that enabled security mechanisms and services remain operational.
- Inform the Security Officer and System Owner of any security-related anomaly, compromise, or vulnerability.
- Monitor the security status of the system.
In the event of information security incidents:
- Register, account for, and manage security incidents within the Systems under their responsibility.
- Execute the approved security plan.
- Isolate the incident to prevent propagation to elements outside the risk situation.
- Make short-term decisions if information has been compromised in a way that could lead to serious consequences (these actions should be reflected in a documented procedure to minimize the System Security Administrator’s margin of discretion).
- Ensure the integrity of critical System elements if their availability has been affected (these actions should be reflected in a documented procedure to minimize the System Security Administrator’s margin of discretion).
- Maintain and recover the information stored by the System and its associated services.
- Investigate the incident: Determine the method, means, motives, and origin of the incident.
F. Physical Security Officer
The Talent & Administration Manager has been designated as the Physical Security Officer. They are responsible for implementing the security measures within their scope, as determined by the Information Security Officer, and shall report to the latter regarding their degree of implementation, effectiveness, and any incidents.
3.1 INFORMATION SECURITY COMMITTEE
The Information Security Committee has been established and will be composed of the following members:
Any other users and/or managers whose intervention is required due to being affected by the National Security Framework (ENS) or the GDPR may attend at the Committee’s request.
The functions of the Information Security Committee are as follows:
- Address the concerns of Senior Management and the different departments.
- Regularly inform Senior Management on the status of information security.
- Promote the continuous improvement of the Information Security Management System (ISMS).
- Develop the organization’s evolution strategy regarding information security.
- Coordinate the efforts of the different areas in information security to ensure that actions are consistent, aligned with the decided strategy, and to avoid duplication.
- Develop (and regularly review) the Information Security Policy for approval by Management.
- Approve information security regulations.
- Develop and approve the training and qualification requirements for administrators, operators, and users from an information security perspective.
- Monitor the main residual risks assumed by the organization and recommend possible actions regarding them.
- Monitor the performance of security incident management processes and recommend possible actions. In particular, ensure the coordination of different security areas in managing information security incidents.
- Promote periodic audits to verify compliance with the organization’s security obligations.
- Approve information security improvement plans for the organization. Specifically, it will ensure the coordination of different plans that may be carried out in various areas.
- Ensure that information security is considered in all ICT projects, from initial specification to operation. In particular, it shall oversee the creation and use of horizontal services that reduce duplication and support the consistent operation of all ICT systems.
- Resolve conflicts of responsibility that may arise between different managers and/or areas of the Organization, escalating cases where it lacks sufficient authority to decide.
- Regularly gather relevant information from internal or external technical staff to make informed decisions.
- Seek advice on matters requiring a decision or an opinion. This advice will be determined on a case-by-case basis and may take various forms:
- Specialized internal, external, or mixed working groups.
- Internal and/or external consultancy.
- Attendance at courses or other training and experience-sharing environments.
In the event of information security incidents:
- Approve the Security Improvement Plan, along with its corresponding budget allocation.
3.2 HIERARCHY IN THE DECISION-MAKING PROCESS AND COORDINATION MECHANISMS
The different information security roles (main authority and possible delegates) are limited to a simple hierarchy: the Information Security Committee provides instructions to the Information Security Officer, who is responsible for fulfillment, supervising that administrators and operators implement security measures in accordance with the Organization’s approved security policy.
The System Security Administrator reports to the System Owner on:
- Incidents regarding system security.
- Configuration, update, or corrective actions
The System Owner informs the Information Owner of functional incidents relating to the information under their responsibility. The System Owner informs the Service Owner of functional incidents relating to the service under their responsibility. The System Owner reports to the Security Officer regarding:
- Security-related actions, particularly regarding system architecture decisions.
- A consolidated summary of security incidents.
- Metrics on the effectiveness of the protection measures to be implemented.
The Security Officer informs the Information Owner of security-related decisions and incidents affecting the information under their responsibility, specifically regarding residual risk estimation and significant risk deviations from approved margins. The Security Officer informs the Service Owner of security-related decisions and incidents affecting the service under their responsibility, specifically regarding residual risk estimation and significant risk deviations from approved margins. When an Information Security Committee exists, the Security Officer reports to said committee as secretary.
3.3 APPOINTMENT PROCEDURES
The Organization’s Management shall formally appoint:
- The Information Owner; which may be an individual position or a collective body (typically, the Information Security Committee).
- The Service Owners; who may be the same as the Information Owner; this may be an individual position or a collective body (typically, the Information Security Committee).
- The Security Officer, who must report directly to Management or, where one exists, to the Information Security Committee.
- The System Owner, who must report directly to Management or, where one exists, to the Information Security Committee.
- The Security/System Administrator, who reports to the Security Officer.
- The Physical Security Officer, who reports to the System Owner.
The Organization’s Management appoints the System Owner as follows:
- Upon the proposal of the Information Owner, when the Information System processes a single type of information.
- Upon the proposal of the Service Owner, when the Information System provides a single service.
- Directly when the Information System processes different types of information or provides multiple services, after consulting with the relevant Information and Service Owners.
The Organization’s Management appoints the System Security Administrator upon the proposal of either the System Owner or the Information Security Officer.
3.4 PERSONAL DATA
To provide the intended services, personal data must be processed. The Record of Processing Activities (ROPA) details the affected processing operations and their corresponding controllers, as well as the measures adopted resulting from the Data Protection Impact Assessments (DPIA) carried out on said processing. All information systems shall comply with the security levels required by regulations, based on the nature and purpose of the personal data collected in the aforementioned Record of Processing Activities.
4. ROLES LINKED TO PERSONAL DATA PROTECTION
4.1 FUNCTIONS AND OBLIGATIONS OF THE DATA CONTROLLER
The Data Controller is the natural or legal person, whether of a public or private nature, or administrative body, who decides on the purpose, content, and use of the processing.
The status of Data Controller has been assigned to the Director of Operations; as such, it is understood that the entity is the Data Controller for the personal data contained within its information systems, which derive from the provision of the public services assigned within its scope of competence.
The functions of the Data Controller are:
- Adopt the necessary technical and organizational measures to guarantee the security of personal data and prevent its alteration, loss, or unauthorized processing or access.
- Inform data subjects of their rights and the terms under which they can exercise them.
- Exclude from processing any data relating to a data subject who objects to the processing of the same.
- Cease the unlawful use or disclosure of data when requested by the data subject.
- Obligation to give effect to the data subject’s right to rectification or erasure within a maximum period of one month.
Notify those to whom personal data has been disclosed of any rectifications or cancellations made, in the event that the latter continues the processing, who must also proceed with the cancellation.
4.2 FUNCTIONS AND RESPONSIBILITIES OF THE DATA PROTECTION OFFICER
The Data Protection Officer (DPO) may be an individual or a collective body, whose duties are outlined in Article 39 of Regulation (EU) 2016/679, as well as Articles 36 and 37 of Organic Law 3/2018. The DPO is responsible for overseeing the application of privacy and data protection legislation within the entity where they perform their duties.
The Data Protection Officer shall have, at a minimum, the following functions:
- To inform and advise the controller or the processor and the employees who carry out processing of their obligations pursuant to this Regulation and to other Union or Member State data protection provisions;
- To monitor compliance with this Regulation, with other Union or Member State data protection provisions and with the policies of the controller or processor in relation to the protection of personal data, including the assignment of responsibilities, awareness-raising and training of staff involved in processing operations, and the related audits;
- To provide advice where requested as regards the data protection impact assessment and monitor its performance pursuant to Article 35;
- To cooperate with the supervisory authority;
- To act as the contact point for the supervisory authority on issues relating to processing, including the prior consultation referred to in Article 36, and to consult, where appropriate, with regard to any other matter.
The Data Protection Officer shall, in the performance of his or her tasks, have due regard to the risk associated with processing operations, taking into account the nature, scope, context and purposes of processing.
To this end, he or she shall be able to:
- Collect information to determine processing activities,
- Analyze and check the compliance of processing activities, and inform, advise and issue recommendations to the controller or the processor.
- Collect information to monitor the record of processing activities.
- Advise on the application of the principle of data protection by design and by default.
- Advise on:
- Whether or not a data protection impact assessment should be carried out.
- What methodology should be followed when conducting a data protection impact assessment.
- Whether the data protection impact assessment should be carried out using internal resources or through external outsourcing.
- What safeguards (including technical and organizational measures) to apply to mitigate any risk to the rights and interests of the data subjects.
- Whether or not the data protection impact assessment has been correctly carried out, and
- Whether its conclusions (whether or not to proceed with the processing and what safeguards to apply) are compliant with the Regulation.
- Prioritize your activities and focus your efforts on those issues that present the greatest risks related to data protection.
- Advise the data controller on:
- What methodology to use when carrying out a data protection impact assessment,
- which areas should be subject to internal or external data protection audits,
- what internal training activities to provide to staff or managers responsible for data processing activities, and which processing operations to dedicate more time and resources to.
The Data Protection Officer (DPO) must possess specialized knowledge of data protection law and practice. Therefore, the necessary knowledge, skills, and abilities that the DPO must possess to perform their duties have been identified.
These general DPO functions can be specified as advisory and supervisory tasks, among others, in the following areas:
a) Compliance with principles relating to data processing, such as purpose limitation, data minimization, and data accuracy.
b)Identification of the legal bases for data processing.
c)Assessment of the compatibility of processing for purposes other than those for which the data was initially collected.
d)Determination of the existence of sector-specific regulations that may establish specific processing conditions different from those established by general data protection regulations.
e)Design and implementation of information measures for data subjects.
f)Establishment of mechanisms for receiving and managing requests to exercise their rights.
g)Assessment of requests to exercise data subjects’ rights.
h)Contracting data processors, including the content of the contracts or legal acts that regulate the controller-processor relationship.
i)Identification of international data transfer instruments appropriate to the organization’s needs and characteristics, and the reasons justifying the transfer.
j)Design and implementation of data protection policies.
k)Data protection audit. Establishment and management of processing activity records.
l)Risk analysis of processing activities.
m)Implementation of data protection measures by design and by default, appropriate to the risks and nature of the processing activities.
n)Implementation of security measures appropriate to the risks and nature of the processing activities.
o)Establishment of procedures for managing data security breaches, including risk assessments for the rights and freedoms of data subjects and procedures for notifying supervisory authorities and data subjects.
p)Determining the need for data protection impact assessments.
q)Conducting data protection impact assessments.
r)Liaison with supervisory authorities.
s)Implementation of staff training and awareness programs on data protection.
4.3 FUNCTIONS AND OBLIGATIONS OF USERS WITH ACCESS TO DATA
All employees of the organization are subject to functions and obligations. All personnel within the organization who have access to personal data must comply with the following obligations:
- The dissemination of personal or confidential data belonging to the organization is prohibited. Users are obligated to maintain the confidentiality of this information even after the employment relationship has ended.
- Users are responsible for reporting all incidents according to the incident management procedure. Failure to report an incident will be considered a breach of duty.
- Users are responsible for all access made using their username and password; therefore, they must not disclose their password.
- Users are responsible for logging out or locking their computer with a password whenever they leave their workstation.
- Applications may not be installed on the organization’s systems without the consent of the Data Protection Officer. Copying personal data onto storage media is not permitted without the express authorization of the data protection officer.
- Users are responsible for storing email information in the appropriate server folders and not indefinitely in their email client.
4.4 FUNCTIONS AND OBLIGATIONS OF THE DATA PROCESSOR
Data processors are responsible for carrying out the ordinary tasks necessary for the effective performance of the functions for which the processing was created on behalf of the Data Controller.
In this regard, Article 4, paragraph 8 of the GDPR defines the Data Processor as the natural or legal person, public authority, agency, or other body which processes personal data on behalf of the data controller.
The Data Processor must implement the necessary technical and organizational measures to ensure the security of personal data and prevent its alteration, loss, unauthorized processing, or access. Likewise, it must implement the security measures referred to in the previous paragraph, which will be stipulated in the contract with the Data Controller.
Specifically, its functions are:
- Process data.
- Perform data processing, quality, and security controls.
- Control the procedures and requirements for adding and deleting data.
- Control security measures.
- Control and manage passwords.
- Maintain an incident log.
- Create a list of situations in which a data subject does not wish their personal data to be stored.
- Forward requests to exercise rights received from data subjects to the data controller.
WOCU MONITORING, S.L. must carry out an updated document where the data processors who are providing services will be identified, as well as the indication of the formalization of the relevant contract with these service providers with access to data.
5 RISK MANAGEMENT
5.1 JUSTIFICATION
All systems subject to this Policy must conduct a risk analysis, assessing the threats and risks to which they are exposed.
The risk analysis will be the basis for determining the security measures that must be adopted in addition to the minimum requirements established by the National Security Framework, as stipulated in Article 6 of the ENS.
5.2 RISK ASSESSMENT CRITERIA
To harmonize risk analyses, the Information Security Committee will establish a benchmark assessment for the different types of information handled and the different services provided.
The detailed risk assessment criteria will be specified in the risk assessment methodology developed by the organization, based on recognized standards and best practices.
At a minimum, all risks that could seriously impede the provision of services or the fulfillment of the organization’s mission must be addressed.
Special priority will be given to risks that could lead to a cessation of service provision to citizens.
5.3 TREATMENT GUIDELINES
The Information Security Committee will streamline the availability of resources to address the security needs of the different systems, promoting horizontal investments.
5.4 RESIDUAL RISK ACCEPTANCE PROCESS
Residual risks will be determined by the Information Security Officer.
The expected residual risk levels for each piece of Information after the implementation of the planned processing options (including the implementation of the security measures outlined in Annex II of the National Security Framework) must be accepted beforehand by the Data Controller.
The expected residual risk levels for each Service after the implementation of the planned processing options (including the implementation of the security measures outlined in Annex II of the National Security Framework) must be accepted beforehand by the Service Manager.
The Information Security Officer will present the residual risk levels to the Information Security Committee, so that it may, if necessary, evaluate, approve, or amend the proposed processing options.
5.5 NEED TO PERFORM OR UPDATE RISK ASSESSMENTS
Risk analysis and mitigation must be a regularly repeated activity, as established in Article 9 of the National Security Framework (ENS). This analysis will be repeated:
- Regularly, at least once a year.
- When significant changes occur in the information handled.
- When significant changes occur in the services provided.
- When significant changes occur in the systems that process information and are involved in the provision of services.
- When a serious security incident occurs.
- When serious vulnerabilities are reported.
6 SECURITY INCIDENT MANAGEMENT
6.1 INCIDENT PREVENTION
Departments must avoid, or at least prevent to the extent possible, the disruption of information or services due to security incidents. The National Security Scheme (ENS), through Article 19, establishes that systems must be designed and configured to ensure security by default. Similarly, Article 17 of the ENS stipulates that systems must be installed in separate areas with access control procedures.
To this end, departments must implement the minimum security measures determined by the ENS, as well as any additional controls identified through a threat and risk assessment. These controls, and the security roles and responsibilities of all personnel, must be clearly defined and documented.
To ensure compliance with the policy, departments must:
- Establish secure areas for critical or confidential information systems.
- Authorize systems before putting them into operation.
- Regularly assess security, including evaluations of routine configuration changes.
- Request periodic third-party reviews to obtain an independent assessment.
6.2 MONITORING AND INCIDENT DETECTION
Since services can degrade rapidly due to incidents, ranging from a simple slowdown to complete shutdown, services must continuously monitor operations to detect anomalies in service delivery levels and act accordingly, as established in Article 9 of the National Security Framework (ENS).
Monitoring is especially relevant when establishing lines of defense in accordance with Article 8 of the ENS. Detection, analysis, and reporting mechanisms will be established to reach the responsible parties regularly and whenever a significant deviation from pre-established normal parameters occurs.
Intrusion detection systems primarily perform a supervisory and auditing role over the Organization’s resources, verifying that the security policy is not violated and attempting to identify any type of malicious activity early and effectively.
6.3 INCIDENT RESPONSE
Departments must:
- Establish mechanisms to respond effectively to security incidents.
- Designate a point of contact for communications regarding incidents detected in other departments or agencies.
- Establish protocols for the exchange of incident-related information. This includes two-way communication with Computer Emergency Response Teams (CERTs).
6.4 INCIDENT RECOVERY AND CONTINUITY PLANS
To ensure the availability of critical services, departments must develop IT systems continuity plans as part of their overall business continuity and recovery plan.
7 STAFF OBLIGATIONS
All members of the organization are obligated to know and comply with this Information Security Policy and the Security Regulations. The Information Security Committee is responsible for ensuring that this information reaches those affected.
At least every two years, and always within the same year as the audit, all members of the organization will attend an ICT security awareness session.
An ongoing awareness program will be established to serve all members of the organization, particularly new hires.
Individuals with responsibility for the use, operation, or administration of ICT systems will receive training on the secure handling of these systems to the extent necessary to perform their work. This training is mandatory before assuming any responsibility, whether it is their first assignment or a change of job or responsibilities within the same position.
Compliance with this Security Policy is mandatory for all internal and external personnel involved in the organization’s processes. Failure to comply constitutes a serious labor-related offense.
8 THIRD PARTIES
When providing services or managing information for other organizations, they will be informed of this Information Security Policy. Channels will be established for reporting and coordinating with their respective Information Security Committees, and procedures will be established for responding to security incidents.
When using third-party services or transferring information to third parties, they will be informed of this Security Policy and the Security Regulations applicable to those services or information. These third parties will be subject to the obligations established in those regulations and may develop their own operating procedures to comply with them.
Specific procedures for reporting and resolving incidents will be established.
It will be ensured that third-party personnel are adequately trained in security matters, at least to the same level as established in this Policy.
When any aspect of the Policy cannot be met by a third party as required in the preceding paragraphs, a report from the Security Officer will be required, specifying the risks involved and how they will be addressed. This report will require approval from those responsible for the information and the affected services before proceeding.
9 REVIEW AND APPROVAL OF THE SECURITY POLICY
The Information Security Policy will be reviewed by the Information Security Committee at planned intervals, which may not exceed one year, or whenever significant changes occur, to ensure its continued suitability, adequacy, and effectiveness.
Changes to the Information Security Policy must be approved by the appropriate higher authority, in accordance with Article 12 of the National Security Framework (ENS).
Any changes to the Policy must be communicated to all affected parties.
10 SUPPLEMENTARY DOCUMENTATION
The Information Security Policy will be supplemented with more detailed documents that help implement its objectives. These will include:
- Security Standards
- Security Guides
- Security Procedures
Standards standardize the use of specific aspects of the system. They indicate the correct use and user responsibilities. They are mandatory.
Guides are educational in nature and aim to help users correctly apply security measures by providing reasoning where precise procedures do not exist. For example, there is usually a guide on how to write security procedures. Guides help prevent overlooking important security aspects that can manifest in various ways.
Security procedures address specific tasks, indicating what needs to be done, step by step. They are useful for repetitive tasks.
ANNEX I. GLOSSARY OF TERMS
Risk Analysis
Systematic use of available information to identify hazards and estimate risks.
Personal Data
Any information concerning identified or identifiable natural persons.
Incident Management
Action plan to address incidents that occur. In addition to resolving them, it must incorporate performance measures that allow for understanding the quality of the protection system and detecting trends before they become major problems.
Risk Management
Coordinated activities to direct and control an organization with respect to risks.
Security Incident
An unexpected or unwanted event with consequences detrimental to the security of the information system.
Information
A specific instance of a certain type of information.
Security Policy
A set of guidelines, documented in writing, that govern how an organization manages and protects information and services it considers critical.
Basic Security Principles
Fundamental principles that should govern all actions aimed at securing information and services. Information Officer
Person with the authority to establish information security requirements.
Security Officer
The security officer will determine the decisions necessary to meet the security requirements of information and services.
Service Manager
Person with the authority to establish the security requirements of a service.
System Manager
Person responsible for operating the information system.
Service
Function or provision performed by an official entity to protect the interests or meet the needs of citizens.
Information System
An organized set of resources that allows information to be collected, stored, processed, maintained, used, shared, distributed, made available, presented, or transmitted.
